XSSFilt: an XSS Filter for Firefox
Introduction
Cross-Site Scripting (XSS) is a web vulnerability that allows a malicious third party to run JavaScript code on the users' browsers with the credentials of a vulnerable site. Even though JavaScript code is sandboxed and does not allow a malicious entity to take over the victim's computer, sensitive data that is associated to the vulnerable website (e.g. passwords, bank login information) can be stolen.
To protect against XSS attacks, we developed XSSFilt, a browser-resident client-side XSS filter. Client-side XSS filters allow users to protect themselves against XSS attacks without any cooperation from websites, and browser-resident filters are more accurate than previous filters, which were implemented using HTTP proxies.
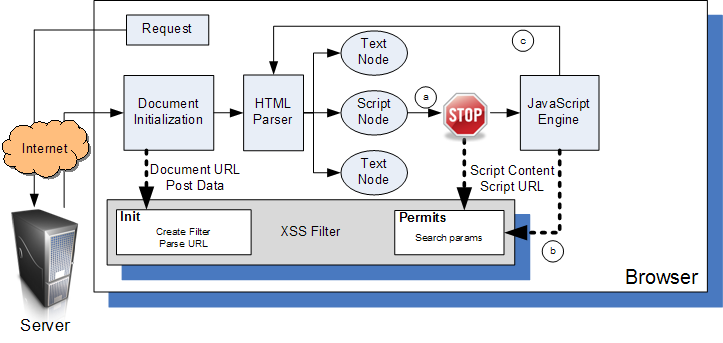
The following picture presents an overview of the architecture. As shown in the picture, all paths that lead to injected JavaScript code being executed are subjected to XSS checks.
Goals
- Protect against reflected XSS attacks without cooperation from websites.
- Low overhead (native C++ implementation)
- Almost no false positives (it should not break existing websites in absence of an actual attack).
- The filter should not rely on user input. Users often do not make sensible decisions when presented with security-related choices.
- The filter should not introduce new vulnerabilities in existing websites (see IE8).
Status
The project has two separate codebases:
- An experimental JavaScript implementation, which served as the reference implementation for an academic publication.
- A native C++ implementation, developed during a Mozilla Corporation internship. The code was submitted to Bugzilla, and underwent code reviews to improve its quality prior to its inclusion in a Firefox alpha version for widespread testing. The process has stalled during the review process.
Download
Both versions are distributed as patches to the mozilla trunk.
The reference implementation is available under the GPL here.
The Mozilla implementation, developed for Firefox 17 (and still awaiting code review), is available at here.
Acknowledgements
This work was supported in part by an an ONR grant N000140710928, an NSF grant CNS-0831298, and an AFOSR grant FA9550-09-1-0539.